Premium Only Content
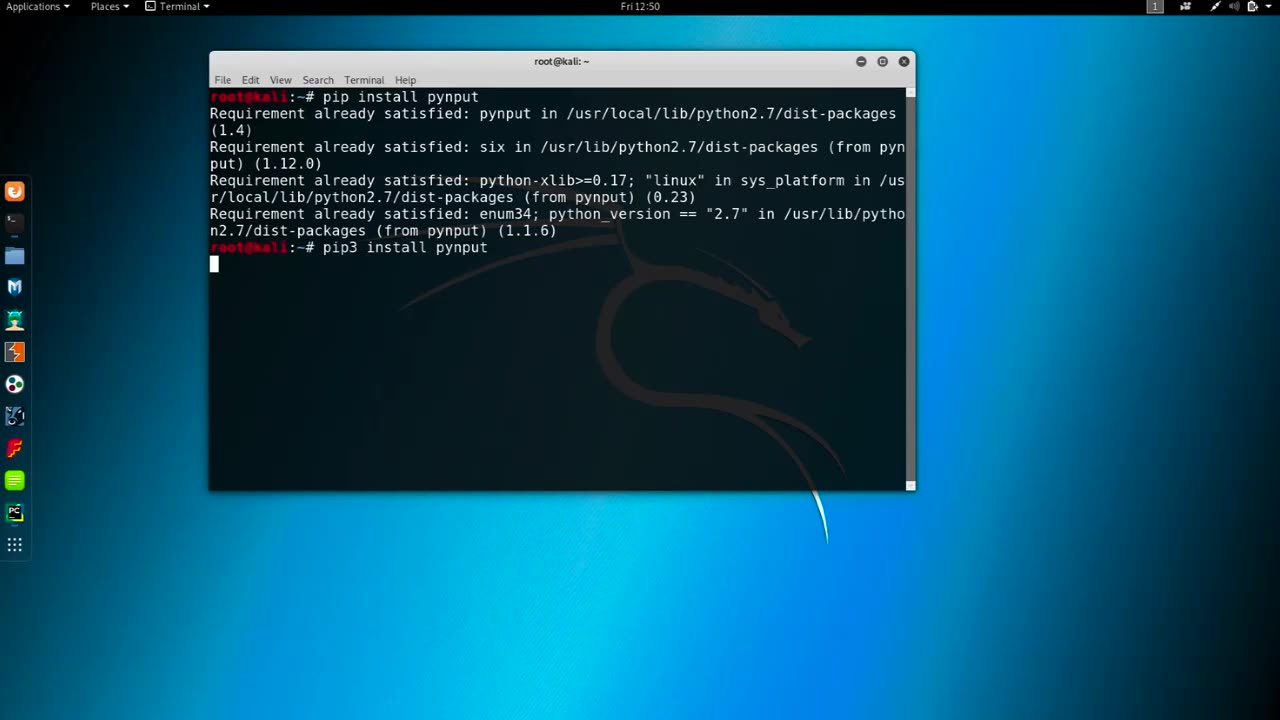
Chapter-37, LEC-4 | Logging Keyboards | #education #ethicalhacking #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Logging keyboards, also known as keyboard loggers or keystroke loggers, are software or hardware devices that capture and record all keystrokes made on a computer or mobile device's keyboard. They are used for monitoring or surveillance purposes and can capture every key pressed, including letters, numbers, special characters, and function keys, as well as other activities such as mouse movements, screenshots, and websites visited.
Keyboard loggers can operate in stealth mode, meaning they can run in the background without the user's knowledge or consent, and log all keystrokes made on the device. They can capture a wide range of information, including passwords, usernames, credit card numbers, chat messages, and other sensitive data that is entered using the keyboard.
Keyboard loggers may be used for both legitimate and malicious purposes. Legitimate uses include monitoring employee activity in the workplace, parental control to monitor children's online activities, and data recovery. However, keyboard loggers can also be used maliciously for stealing personal information, committing identity theft, financial fraud, and other cybercrimes.
It is essential to note that using keyboard loggers without proper authorization is illegal in many jurisdictions, and ethical considerations should always be taken into account when using them for any purpose. Users should always be informed and give explicit consent before their activities are monitored, and appropriate security measures should be in place to protect the data collected by keyboard loggers.
It is important to use keyboard loggers responsibly and within the legal and ethical boundaries, ensuring that privacy rights are respected, and data security is maintained at all times. Proper consent, transparency, and compliance with applicable laws and regulations are crucial when using keyboard loggers for any purpose.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 LIVE
LIVE
BEK TV
22 hours agoTrent Loos in the Morning - 10/03/2025
551 watching -
 LIVE
LIVE
The Bubba Army
21 hours agoDiddy BEGS for Mercy in Judge Letter - Bubba the Love Sponge® Show | 10/03/25
2,682 watching -
 LIVE
LIVE
ZENNY
2 hours agoBO7 IS HERE BOT POV MF HAHAHAHA 6v6 PG18+ | UNFILTERED CHAT | CURSES AND BAD
120 watching -
 15:17
15:17
Actual Justice Warrior
2 days agoBLM Leader CONVICTED Of Fraud
15.5K32 -
 13:19
13:19
Zoufry
2 days agoThe Grandpa Gang Who Robbed a Bang For $16 Million
14.4K4 -
 2:18:45
2:18:45
The China Show
3 days agoChinese Citizens STRIKE BACK + China's Sick New Punishment Exposed - #282
17.5K5 -
 25:20
25:20
The Chris Cuomo Project
1 day agoChris Cuomo EXPOSES Lies Behind the Government Shutdown
16.3K44 -
 21:03
21:03
Nate The Lawyer
1 day ago $3.25 earnedChicago Mayor Brandon Johnson Under Fire Over ‘Defund’ Remarks Amid Crime Concerns
19.9K13 -
 8:05
8:05
MattMorseTV
18 hours ago $12.97 earnedSchumer’s SECRET AGENDA just got EXPOSED.
50.8K49 -
 16:37
16:37
Robbi On The Record
12 hours ago $3.07 earnedThe Theater of Manufactured Outrage - When Left and Right Dance for the Same Puppet Master
16.1K7
