Premium Only Content
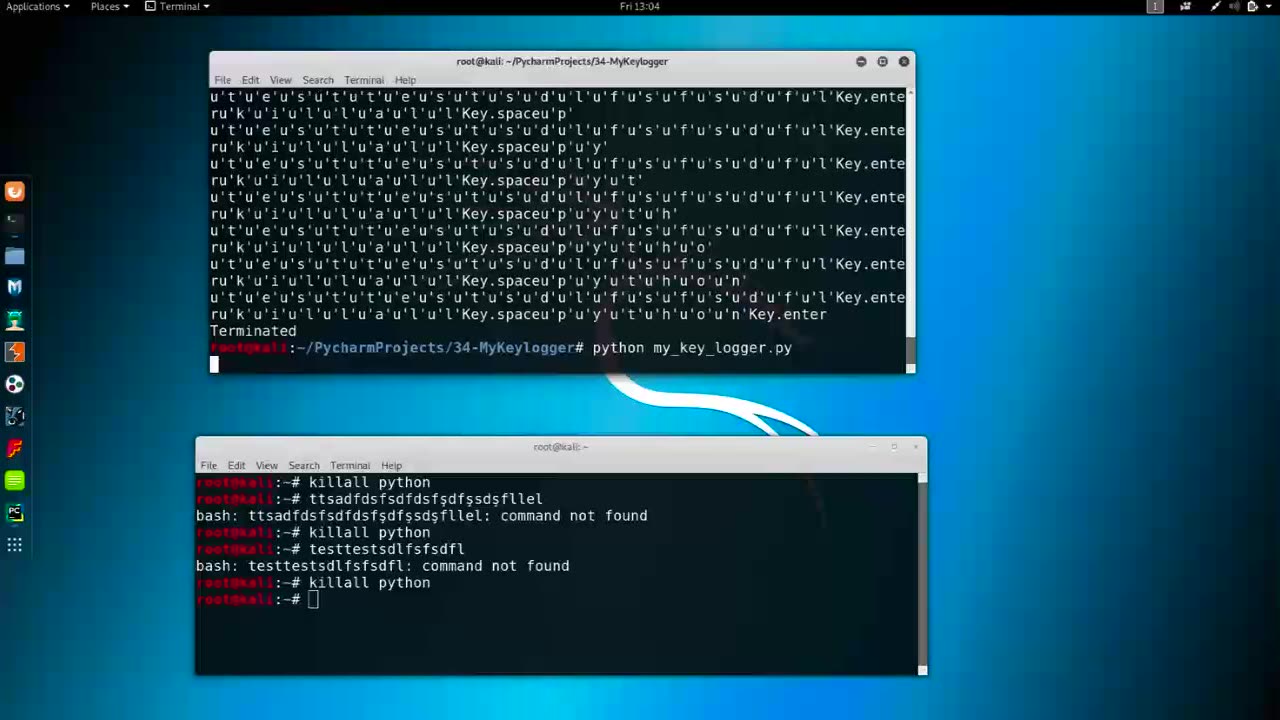
Chapter-37, LEC-5 | Saving Logs | #shackingup #hackinghealth #growthhackingtips #wifihacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Saving logs refers to the process of recording and storing data logs or records generated by various software applications, systems, or devices for later analysis, monitoring, or archival purposes. Logs are chronological records that capture information about events, activities, or transactions, and they can be generated by various types of software, hardware, or systems, including operating systems, databases, web servers, network devices, and applications.
The process of saving logs typically involves several steps:
Logging data generation: Logs are automatically generated by software or hardware systems when certain events or activities occur, such as system errors, user interactions, data transactions, or security events. These logs can contain various types of information, including timestamps, user actions, error messages, system status, or other relevant details depending on the context.
Log collection: Logs are collected from various sources and centralized in a designated location, such as a log server or a log management system. This can involve gathering logs from different devices or systems, aggregating them into a central repository, and storing them securely to ensure data integrity and confidentiality.
Log storage: Logs are stored in a format that allows for easy retrieval, analysis, and monitoring. This may involve storing logs in text files, databases, or specialized log storage solutions that provide efficient and scalable storage options for large volumes of log data.
Log retention: Logs may be retained for a specific period of time, depending on regulatory requirements, business needs, or security policies. Organizations may have retention policies in place to determine how long logs should be stored before being purged or archived to comply with legal or industry regulations.
Log analysis: Logs can be analyzed to gain insights, detect patterns, identify anomalies, troubleshoot issues, or monitor system performance. Log analysis can involve manual review, automated tools, or machine learning algorithms to extract meaningful information from the logs and identify trends, anomalies, or potential security breaches.
Log backup: Logs may be backed up regularly to protect against data loss due to hardware failures, software errors, or other issues. Backups of logs are typically stored in separate locations to ensure data redundancy and availability in case of emergencies.
Proper management of logs is critical for maintaining system integrity, identifying and resolving issues, ensuring compliance with regulations, and supporting forensic investigations. Organizations should have proper policies and procedures in place for saving logs, including data retention, backup, security, and privacy considerations, to ensure effective log management practices.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 LIVE
LIVE
The Chris Salcedo Show
18 hours agoVoters Must REMOVE ALL Ineffective Republicans In The Primary
660 watching -
 1:30:46
1:30:46
Game On!
17 hours ago $0.47 earnedIs This The Start of a DYNASTY For The Seattle Seahawks?
7.17K2 -
 12:05
12:05
VSOGunChannel
18 hours ago $0.85 earnedCalifornia Attacks the Internet & 3D Printing
9.18K4 -
 2:05:10
2:05:10
BEK TV
1 day agoTrent Loos in the Morning - 2/10/2026
18.7K1 -
 11:17
11:17
Actual Justice Warrior
15 hours agoBlack Restaurant Gets ROBBED Immediately After Opening
60.8K37 -
 34:09
34:09
ZeeeMedia
16 hours agoEpstein Death Statement Drafted Day Before His 'Death' | Daily Pulse Ep 193
35.4K19 -
 2:01:22
2:01:22
MG Show
21 hours agoEpstein Files Explode: Bannon, Byrne, Flynn & Powell Epstein Ties Exposed; Deep State in Panic?
38.4K51 -
 9:02
9:02
Nate The Lawyer
4 days ago $2.29 earnedHenyard Update - Police Chief Pleads Guilty & Rats To FBI On Super Mayor
33.3K9 -
 3:24:41
3:24:41
FreshandFit
16 hours agoShe Left A Great Situation. We Find Out Why! w/ Luke Belmar
299K47 -
 1:34:15
1:34:15
Badlands Media
19 hours agoBaseless Conspiracies Ep. 171: The Lady Bird Lake Murder Mystery
106K36