Premium Only Content
Chapter-38, LEC-4 | Running Commands | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
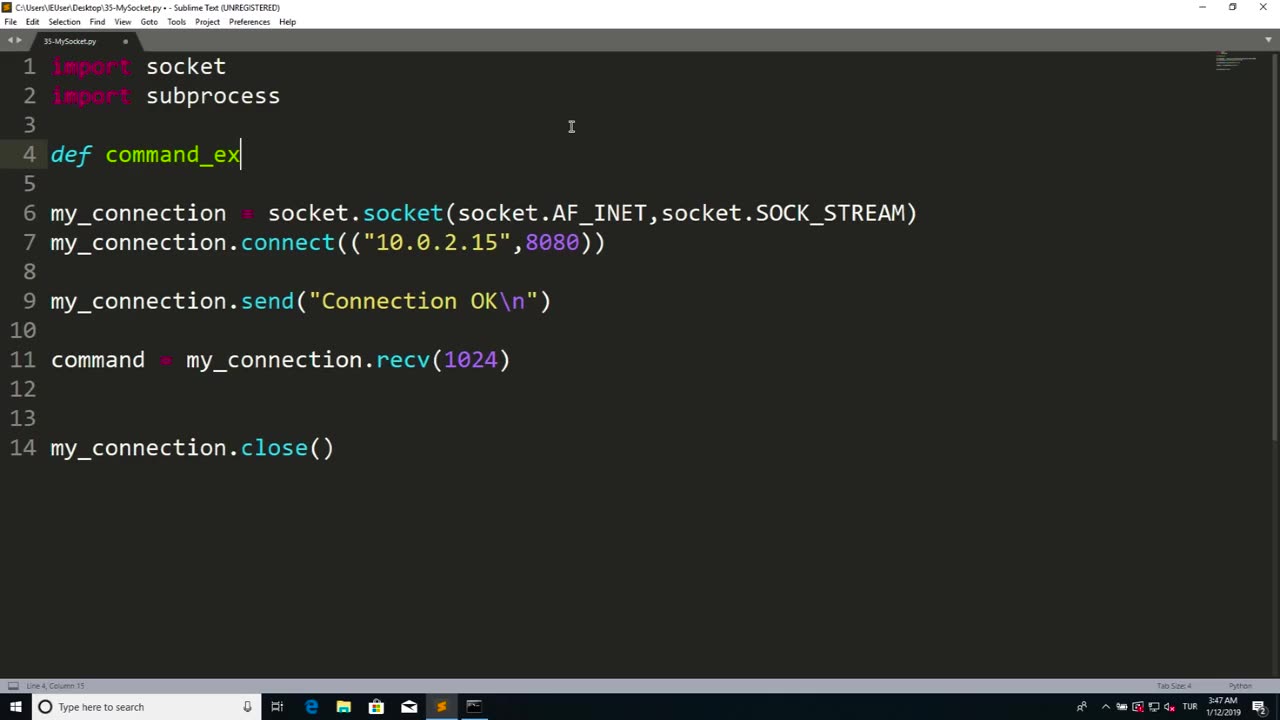
Running commands refers to the process of executing instructions or commands in a computer system or software to perform specific tasks or operations. Commands are typically entered into a command-line interface or terminal, which allows users to interact with a computer system directly through text-based commands.
Running commands can be used for a wide range of purposes, including system administration, software configuration, troubleshooting, automation, and more. Commands can be used to manipulate files and directories, configure settings, install or uninstall software, manage processes, retrieve information, and perform other operations depending on the specific software or system being used.
Running commands requires knowledge of the specific command syntax, options, and parameters for the software or system being used. It is important to understand the implications and potential consequences of the commands being executed, as they can impact the performance, stability, and security of the system or software.
Proper caution and authorization must be exercised when running commands, as some commands may have elevated privileges and can potentially cause harm or damage to the system or data if used improperly or without proper authorization. It is essential to follow best practices, such as using appropriate permissions, verifying the source and integrity of commands, and testing commands in a safe and controlled environment.
Running commands can be a powerful tool in managing computer systems and software efficiently and effectively. However, it requires knowledge, expertise, and responsible use to ensure that commands are executed safely and securely, and that the intended tasks or operations are performed accurately and without any unintended consequences. Always exercise caution, follow proper authorization procedures, and adhere to best practices when running commands in any computer system or software environment.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 LIVE
LIVE
ZENNY
2 hours agoBO7 IS HERE BOT POV MF HAHAHAHA 6v6 PG18+ | UNFILTERED CHAT | CURSES AND BAD
122 watching -
 15:17
15:17
Actual Justice Warrior
2 days agoBLM Leader CONVICTED Of Fraud
15.5K32 -
 13:19
13:19
Zoufry
2 days agoThe Grandpa Gang Who Robbed a Bang For $16 Million
14.4K4 -
 2:18:45
2:18:45
The China Show
3 days agoChinese Citizens STRIKE BACK + China's Sick New Punishment Exposed - #282
17.5K5 -
 25:20
25:20
The Chris Cuomo Project
1 day agoChris Cuomo EXPOSES Lies Behind the Government Shutdown
16.3K44 -
 21:03
21:03
Nate The Lawyer
1 day ago $3.25 earnedChicago Mayor Brandon Johnson Under Fire Over ‘Defund’ Remarks Amid Crime Concerns
19.9K13 -
 8:05
8:05
MattMorseTV
18 hours ago $12.97 earnedSchumer’s SECRET AGENDA just got EXPOSED.
50.8K49 -
 16:37
16:37
Robbi On The Record
12 hours ago $3.07 earnedThe Theater of Manufactured Outrage - When Left and Right Dance for the Same Puppet Master
16.1K7 -
 14:31
14:31
Sponsored By Jesus Podcast
20 hours agoSATAN Knows Scripture Better Than You | Reading the Bible
15.5K5 -
 2:50:36
2:50:36
Side Scrollers Podcast
20 hours agoMore Violent Attacks on Speakers + Hollywood DEMANDS “Free Speech” + More | Side Scrollers
21.2K17
