Premium Only Content
Chapter-38, LEC-4 | Running Commands | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
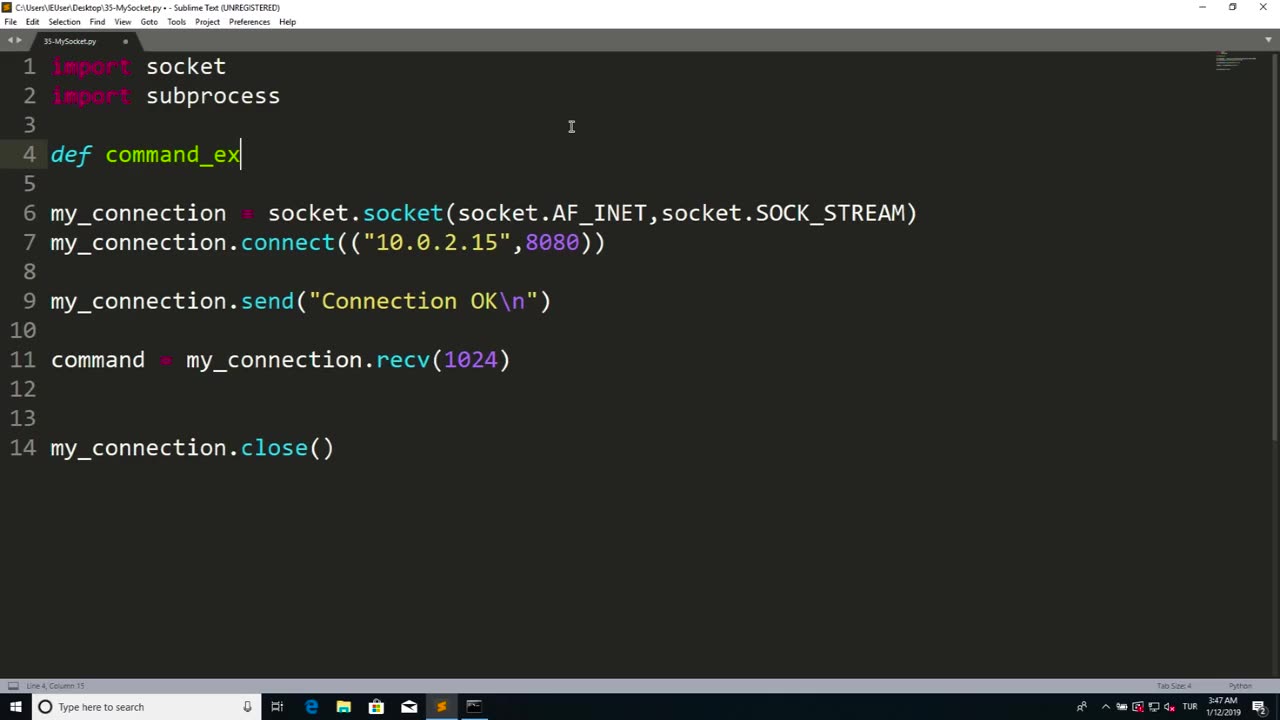
Running commands refers to the process of executing instructions or commands in a computer system or software to perform specific tasks or operations. Commands are typically entered into a command-line interface or terminal, which allows users to interact with a computer system directly through text-based commands.
Running commands can be used for a wide range of purposes, including system administration, software configuration, troubleshooting, automation, and more. Commands can be used to manipulate files and directories, configure settings, install or uninstall software, manage processes, retrieve information, and perform other operations depending on the specific software or system being used.
Running commands requires knowledge of the specific command syntax, options, and parameters for the software or system being used. It is important to understand the implications and potential consequences of the commands being executed, as they can impact the performance, stability, and security of the system or software.
Proper caution and authorization must be exercised when running commands, as some commands may have elevated privileges and can potentially cause harm or damage to the system or data if used improperly or without proper authorization. It is essential to follow best practices, such as using appropriate permissions, verifying the source and integrity of commands, and testing commands in a safe and controlled environment.
Running commands can be a powerful tool in managing computer systems and software efficiently and effectively. However, it requires knowledge, expertise, and responsible use to ensure that commands are executed safely and securely, and that the intended tasks or operations are performed accurately and without any unintended consequences. Always exercise caution, follow proper authorization procedures, and adhere to best practices when running commands in any computer system or software environment.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 51:23
51:23
Donald Trump Jr.
5 hours agoRighting the Left’s Wrongs, Plus Explosive 2020 Revelations | Triggered Ep.315
169K75 -
 LIVE
LIVE
The Jimmy Dore Show
3 hours agoMassie Set to “Go Nuclear” On Trump DOJ! Bill Maher APOLOGIZES to QAnon! w/ Matthew Cormier
8,283 watching -
 14:14
14:14
Robbi On The Record
2 months ago $18.36 earnedThe Identity Crisis No One Wants to Admit | Identity VS. Personality
102K26 -
 1:52:59
1:52:59
Kim Iversen
5 hours agoNew Evidence: Jeffrey Epstein Is ALIVE and in Israel
124K93 -
 LIVE
LIVE
Akademiks
2 hours agoBad Bunny Performs at Superbowl! Cardi B leaves Steffon Diggs? YB or CB to headline next year?
1,111 watching -
 13:41:47
13:41:47
LFA TV
23 hours agoLIVE & BREAKING NEWS! | MONDAY 2/9/26
266K19 -
 1:06:26
1:06:26
The Amber May Show
7 hours ago $1.20 earnedTil You Can’t: Patriot Spirit, Family Legacy & The All-American Halftime Show with Sam Anthony
25.8K4 -
 1:38:27
1:38:27
Redacted News
5 hours agoUnredacted Epstein Files RELEASED to Congress & Epstein's Killer About to Be Revealed? | Redacted
157K145 -
 1:41:05
1:41:05
Russell Brand
8 hours agoRoblox ICE Raids, God and Country, and the Epstein–Israel Connection — SF680
172K29 -
 3:52:14
3:52:14
Decoy
5 hours agoThey're hiding this
46.4K3