Premium Only Content
Chapter-38, LEC-4 | Running Commands | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
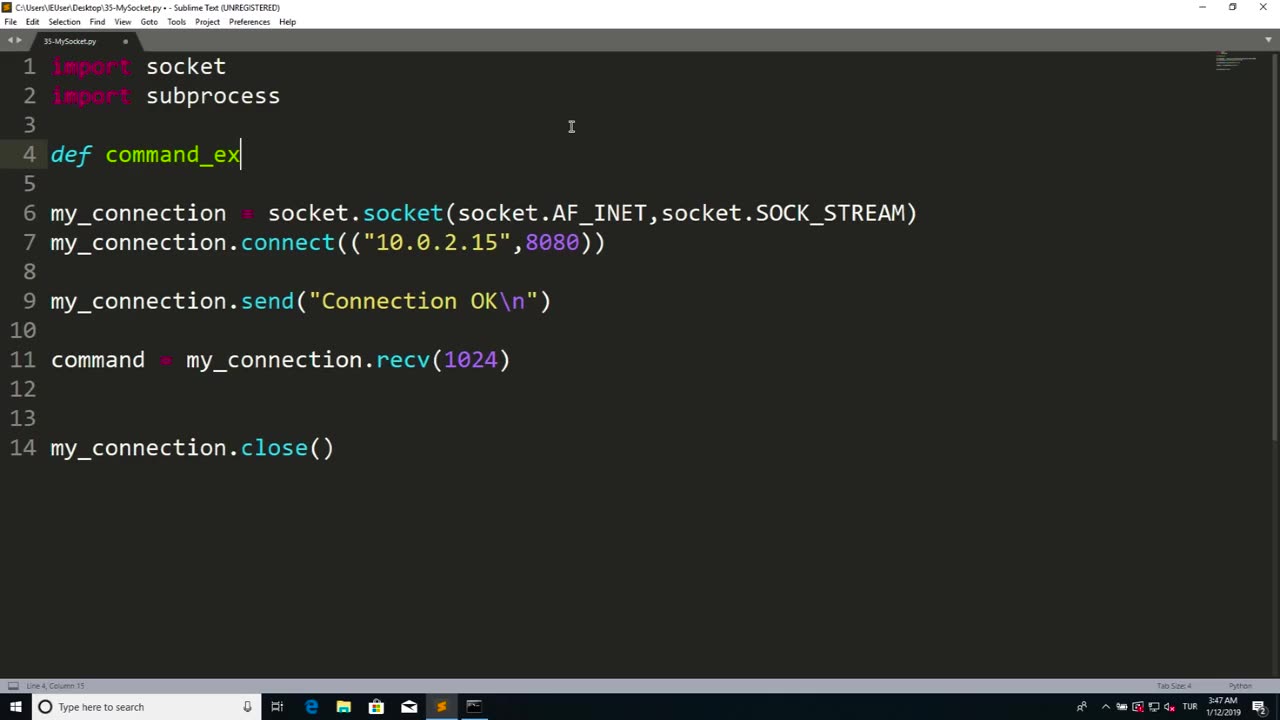
Running commands refers to the process of executing instructions or commands in a computer system or software to perform specific tasks or operations. Commands are typically entered into a command-line interface or terminal, which allows users to interact with a computer system directly through text-based commands.
Running commands can be used for a wide range of purposes, including system administration, software configuration, troubleshooting, automation, and more. Commands can be used to manipulate files and directories, configure settings, install or uninstall software, manage processes, retrieve information, and perform other operations depending on the specific software or system being used.
Running commands requires knowledge of the specific command syntax, options, and parameters for the software or system being used. It is important to understand the implications and potential consequences of the commands being executed, as they can impact the performance, stability, and security of the system or software.
Proper caution and authorization must be exercised when running commands, as some commands may have elevated privileges and can potentially cause harm or damage to the system or data if used improperly or without proper authorization. It is essential to follow best practices, such as using appropriate permissions, verifying the source and integrity of commands, and testing commands in a safe and controlled environment.
Running commands can be a powerful tool in managing computer systems and software efficiently and effectively. However, it requires knowledge, expertise, and responsible use to ensure that commands are executed safely and securely, and that the intended tasks or operations are performed accurately and without any unintended consequences. Always exercise caution, follow proper authorization procedures, and adhere to best practices when running commands in any computer system or software environment.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 2:55
2:55
From Zero → Viral with AI
1 day ago $0.47 earnedAI Misconceptions: Why Small Businesses Hold the Real Advantage 🚀
11.8K -
 LIVE
LIVE
BEK TV
23 hours agoTrent Loos in the Morning - 9/25/2025
165 watching -
 2:39
2:39
The Official Steve Harvey
1 day ago $0.91 earnedThese books didn’t just change my mind, they changed my life. 📚💯
16.4K -
 1:35:35
1:35:35
Investigate Everything w/ Brian O'Shea
14 hours agoPart 1: "Evil & Logistics: Why is the Left So Good At Both” w/ Brian O’Shea & Bill Stebbins
19.8K3 -
 1:20:31
1:20:31
CharLee Simons presents DO NOT TALK
1 day agoR.I.P. MEDIA FREAKS
15.3K1 -
 16:39
16:39
Professor Nez
20 hours ago🚨PRICELESS: Trump Just EMBARRASSED Macron in New York
90.9K21 -
 25:51
25:51
DeVory Darkins
19 hours ago $7.27 earnedDemocrats ghosted and stunned by Trump as Routh attempts to off himself after guilty verdict
27.2K65 -
 21:15
21:15
Actual Justice Warrior
16 hours agoJimmy Kimmel DECLARES Victory
41.9K46 -
 49:42
49:42
Liz Wheeler
18 hours agoWHO is Behind ANTIFA? | Ep 176
44.2K26 -
 8:30
8:30
MattMorseTV
19 hours ago $10.38 earnedThis just ENDED Newsom's CAREER.
174K69