Premium Only Content
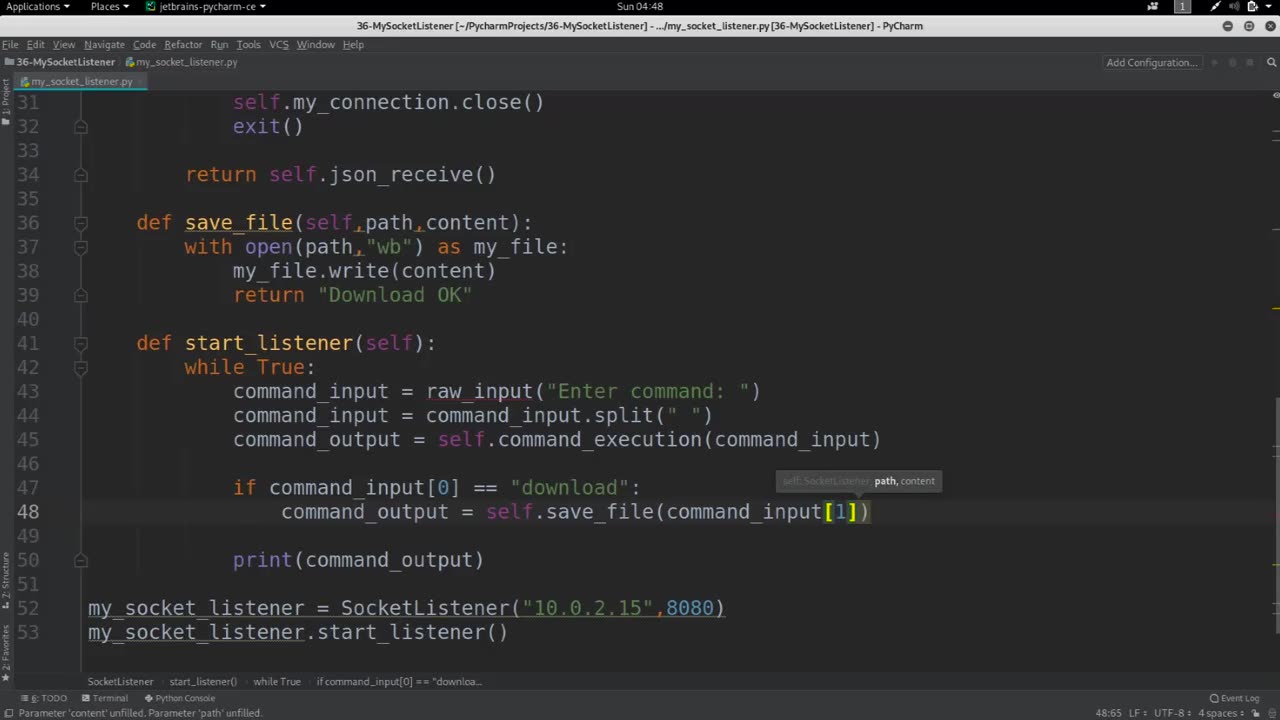
Chapter-38, LEC-14 | Saving Files | #ethicalhacking #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
"Saving Files" refers to the process of creating, writing, and storing data into a file on a computer system or a storage device. This process involves several steps to ensure that the data is correctly written and stored in the desired format and location.
Here's a general description of how "Saving Files" can be implemented:
Creating a file: The first step in saving files is creating a new file or opening an existing file for writing. This may involve specifying the file name, location, and desired file format, and creating a file object or file handle in the programming language or operating system being used.
Writing data: Once the file is created, the implementation of "Saving Files" typically involves writing data into the file. This may involve using appropriate methods or functions to write data in the desired format, such as text, binary, or serialized data. The data may be sourced from various input streams or variables, and it may be written sequentially or in chunks depending on the requirements.
Formatting data: Before writing data into the file, the implementation of "Saving Files" may involve formatting the data according to the desired format or structure. This may involve converting data types, encoding data in a specific character encoding or binary format, and arranging data in a structured format such as JSON, XML, CSV, or other custom formats.
Handling errors and exceptions: The implementation of "Saving Files" should include proper error handling and exception management to handle cases where the file writing process fails due to various reasons, such as file permission issues, disk full errors, or data format errors. This may involve checking for error codes, handling exceptions, and providing appropriate error messages or fallback mechanisms.
Closing the file: Once the data is written into the file, the implementation of "Saving Files" typically involves closing the file to ensure that the data is properly saved and the file resources are released. This may involve closing the file object or file handle, flushing any buffers, and committing any changes to disk.
Verifying file integrity: After saving the file, the implementation of "Saving Files" may involve verifying the integrity of the saved file to ensure that the data has been correctly written and stored. This may involve comparing the written data with the original data, performing checksums or hash functions on the file, or performing other validation checks.
Handling file management tasks: Depending on the specific requirements of the task, the implementation of "Saving Files" may involve additional file management tasks, such as setting file permissions, renaming files, moving files to different directories, or deleting files as needed.
The implementation of "Saving Files" can vary depending on the programming language, operating system, and specific requirements of the task. It may involve steps such as creating a file, writing data, formatting data, handling errors, closing the file, verifying file integrity, and handling file management tasks as needed. Proper implementation should include error handling, resource management, and adherence to relevant coding standards or best practices to ensure reliable and secure file saving functionality.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 46:26
46:26
Sarah Westall
10 hours agoWhat’s Behind the Silver Surge? Large Institutions Cashing In w/ Andy Schectman
40.4K3 -
 6:42:10
6:42:10
Turning Point USA
15 hours agoLIVE NOW: AMFEST DAY 2 - VIVEK, JACK POSOBIEC, MEGYN KELLY, ALEX CLARK AND MORE…
1.29M180 -
 1:14:37
1:14:37
Flyover Conservatives
1 day agoHow to Win 2026 Before It Starts — Clay Clark’s Goal-Setting Blueprint | FOC Show
39.9K1 -
 12:52
12:52
The Kevin Trudeau Show Limitless
2 days agoBeyond Good And Bad: The Hidden Reality Code
84.5K21 -
 1:03:11
1:03:11
BonginoReport
11 hours agoBrown U Security Failures EXPOSED - Nightly Scroll w/ Hayley Caronia (Ep.201)
159K47 -
 51:09
51:09
Patriots With Grit
7 hours agoWill A.I. Replace Doctors? | Dr. Stella Immanuel MD
26.8K4 -
 4:10:32
4:10:32
Nerdrotic
12 hours ago $15.34 earnedHollywood's DOOMSDAY! WB FIRESALE! - Friday Night Tights 385 w Zachary Levi
86.2K19 -
 12:25:53
12:25:53
LFA TV
1 day agoLIVE & BREAKING NEWS! | FRIDAY 12/19/25
206K31 -
 1:08:59
1:08:59
Edge of Wonder
9 hours agoNASA’s Intergalactic Spacecraft, Real Dwarves Spotted & Research Roundup
29.9K7 -
 1:21:27
1:21:27
Kim Iversen
12 hours agoPutin Says Russia is Ready for WAR With Europe
49.6K103