Premium Only Content
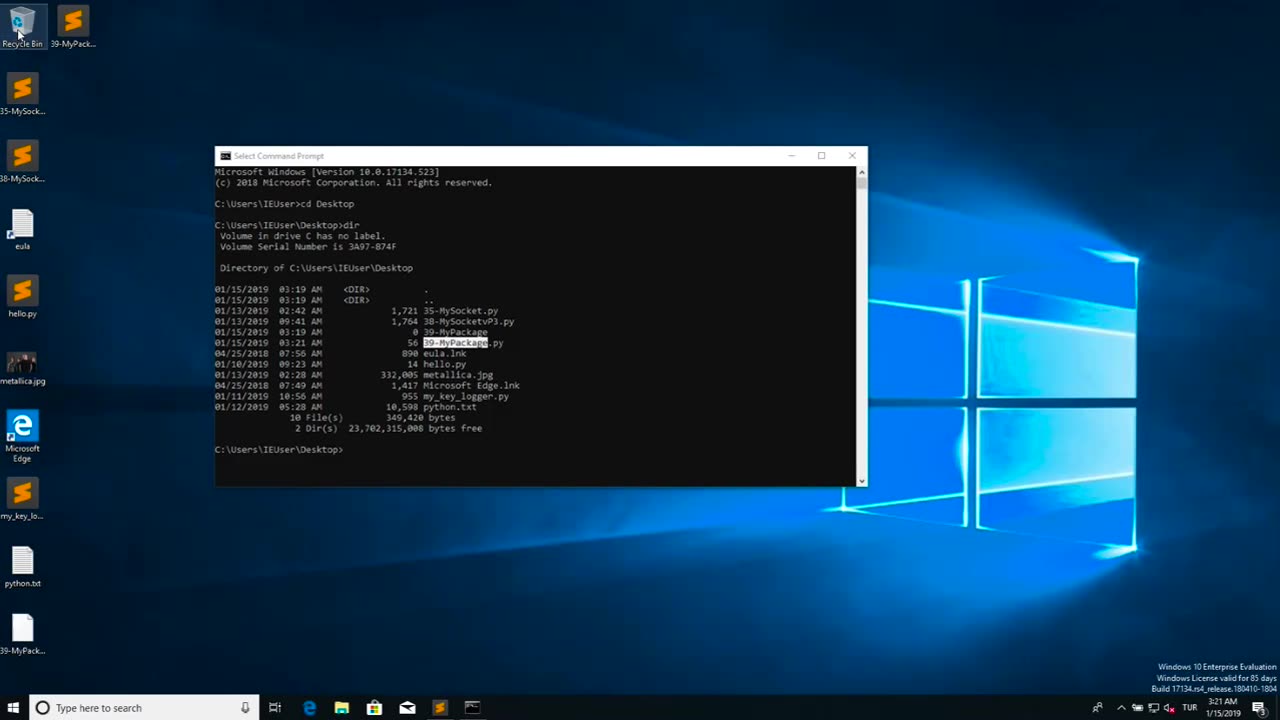
Chapter-39, LEC-2 | Malicious Files | #ethicalhacking #maliciousdiles #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Malicious files refer to digital files, such as software programs or documents, that are intentionally designed to harm or compromise the security of a computer, network, or device. These files may contain malicious code, also known as malware, which can be executed or triggered to perform malicious activities without the knowledge or consent of the user.
Malicious files can come in various forms, including viruses, worms, Trojans, ransomware, spyware, adware, and other types of malware. They are typically disguised as legitimate files or software to deceive users into downloading or executing them. Once the malicious file is executed or opened, it can spread throughout the system, exploit vulnerabilities, steal sensitive information, disrupt operations, or cause other types of damage.
Malicious files are often distributed through various means, such as infected email attachments, compromised websites, infected USB drives, social engineering tactics, and other methods. They can target any type of device or operating system, including computers, servers, smartphones, tablets, and IoT (Internet of Things) devices.
The consequences of encountering and executing malicious files can be severe, ranging from data breaches and financial loss to privacy violations, system downtime, and reputational damage. Therefore, it is crucial to implement robust cybersecurity measures, such as using antivirus software, keeping software and systems updated, being cautious while downloading or opening files, and practicing safe online behavior, to protect against malicious files and other cyber threats.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 LIVE
LIVE
The Quartering
1 hour agoTRUMP VINDICATED IN NEW EPSTEIN DROP, SUPER BOWL BACKLASH GETS WORSE, FBI RELEASES GUTHRIE PHOTO
7,277 watching -
 DVR
DVR
Stephen Gardner
44 minutes ago40 MISSING BALLOT BOXES in Georgia: What They Did to Trump Will Shock You
5 -
 1:04:15
1:04:15
DeVory Darkins
2 hours agoDemocrats EXPLODE after Todd Lyons issues REALITY CHECK regard ICE
119K20 -
 57:11
57:11
The White House
2 hours agoPress Briefing by the White House Press Secretary Karoline Leavitt
25.1K15 -
 58:49
58:49
Timcast
3 hours agoEveryone Is CRASHING OUT Over The Super Bowl Halftime Show
164K54 -
 1:09:55
1:09:55
BonginoReport
3 hours agoDEI will NEVER Make America Great! - Scrolling w/ Hayley (Ep. 232) - 02/10/26
91.5K43 -
 2:59:40
2:59:40
Wendy Bell Radio
7 hours agoSo Many Smokescreens
42.5K86 -
 1:19:29
1:19:29
Sean Unpaved
4 hours agoCan Klint Kubiak SAVE The Las Vegas Raiders? | UNPAVED
16.5K -
 1:48:04
1:48:04
MattMorseTV
3 hours ago $12.60 earned🔴MASSIVE White House PRESS CONFERENCE.🔴
37.2K100 -
 2:30:41
2:30:41
Side Scrollers Podcast
4 hours agoSide Scrollers Podcast Live | Tuesday February 10th 2026
26.4K10