Premium Only Content
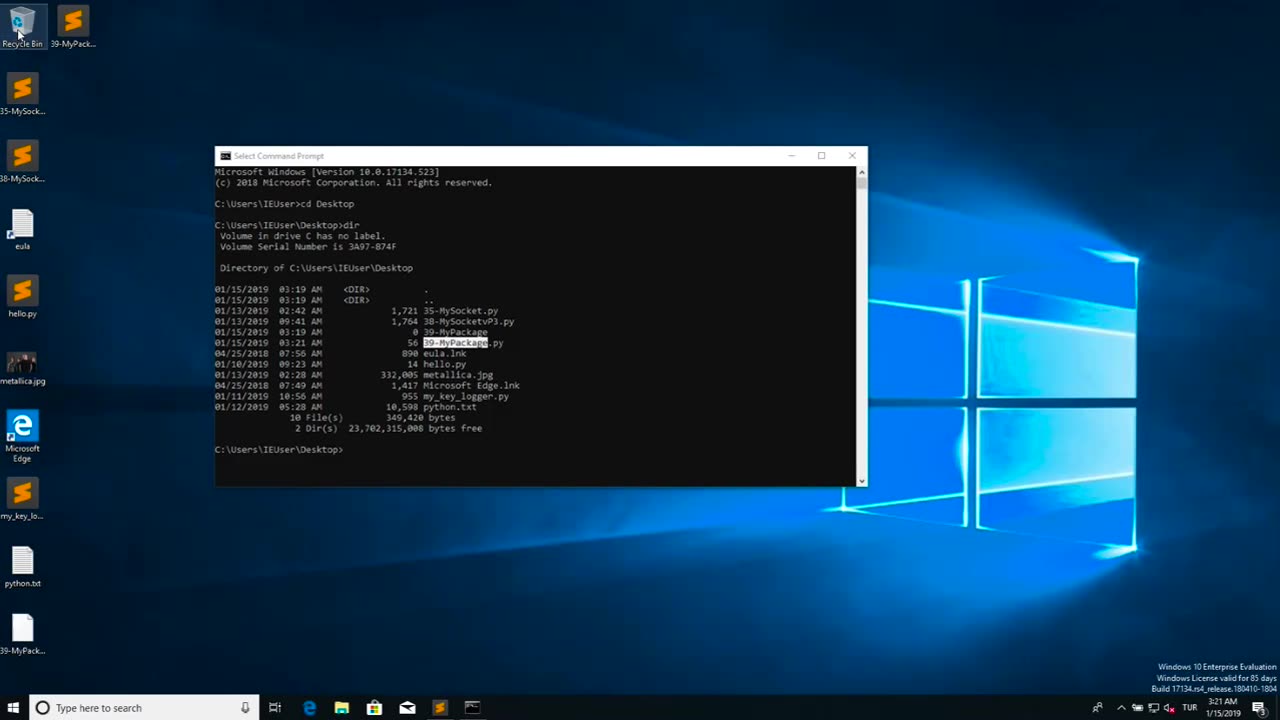
Chapter-39, LEC-2 | Malicious Files | #ethicalhacking #maliciousdiles #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Malicious files refer to digital files, such as software programs or documents, that are intentionally designed to harm or compromise the security of a computer, network, or device. These files may contain malicious code, also known as malware, which can be executed or triggered to perform malicious activities without the knowledge or consent of the user.
Malicious files can come in various forms, including viruses, worms, Trojans, ransomware, spyware, adware, and other types of malware. They are typically disguised as legitimate files or software to deceive users into downloading or executing them. Once the malicious file is executed or opened, it can spread throughout the system, exploit vulnerabilities, steal sensitive information, disrupt operations, or cause other types of damage.
Malicious files are often distributed through various means, such as infected email attachments, compromised websites, infected USB drives, social engineering tactics, and other methods. They can target any type of device or operating system, including computers, servers, smartphones, tablets, and IoT (Internet of Things) devices.
The consequences of encountering and executing malicious files can be severe, ranging from data breaches and financial loss to privacy violations, system downtime, and reputational damage. Therefore, it is crucial to implement robust cybersecurity measures, such as using antivirus software, keeping software and systems updated, being cautious while downloading or opening files, and practicing safe online behavior, to protect against malicious files and other cyber threats.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 8:50
8:50
Sideserf Cake Studio
21 hours ago $4.47 earnedPillow Cat Cake Challenge! (Gabby's Dollhouse Ready to Party)
32.5K7 -
 UPCOMING
UPCOMING
Misfits Mania
3 days agoMISFITS MANIA: Fight Night
109K67 -
 13:14
13:14
Upper Echelon Gamers
20 hours ago $0.85 earnedThe "Slop YouTubers" Are Angry... (And the Reason is Hilarious)
3.84K6 -
 1:06:28
1:06:28
A Cigar Hustlers Podcast Every Day
1 day agoHustler Every Week Day Episode 433 "Oscars And Chill"
7.2K -
 4:26
4:26
GreenMan Studio
1 day agoGREENMANS STOCKING STUFFERS 5 – GREENMAN AI
4.45K5 -
 5:00
5:00
SethDrums
4 days ago $7.91 earnedStaind – It's Been Awhile if it was 1980s
62.8K13 -
 20:18
20:18
itsSeanDaniel
2 days agoCandace Owens CALLED OUT by Piers Morgan, So She FIRES BACK
18.1K14 -
 4:57:14
4:57:14
Akademiks
12 hours ago21 Savage Wants Young Thug, Wham & Gunna to SQUASH IT! Future Sneak Dissing? Jim Jones Pays 50 Cent?
391K13 -
 6:01:38
6:01:38
Right Side Broadcasting Network
2 days agoLIVE: President Trump to Deliver Remarks in Rocky Mount, NC - 12/19/25
148K62 -
 3:24:48
3:24:48
VapinGamers
11 hours ago $49.16 earnedDestiny 2 - Dungeons and Loot with Friends - !rumbot !music
113K1