Premium Only Content
![Leaking Secret Data with a Heap Overflow - "Leek" Pwn Challenge [Angstrom CTF 2023]](https://1a-1791.com/video/s8/1/T/3/u/s/T3usj.qR4e-small-Leaking-Secret-Data-with-a-.jpg)
Leaking Secret Data with a Heap Overflow - "Leek" Pwn Challenge [Angstrom CTF 2023]
Video walkthrough for the binary exploitation (pwn) challenge, "Leek" from the Angstrom capture the flag (CTF) competition 2023. The challenge involves performing a heap overflow to overwrite all null bytes between our user input chunk and secret data chunk so that when puts() is called, it prints both chunks (there's no null terminator separating them). After this, we need to repair the header of the chunk we modified so that the program can continue execution. We repeat this process of leaking and submitting the random (secret) bytes 100 times, at which point we receive the flag! Write-ups/tutorials aimed at beginners - Hope you enjoy 🙂 #Angstrom #AngstromCTF #CTF #Pentesting #OffSec #Pwn #BinaryExploitation #Reversing #ReverseEngineering
↢Social Media↣
Twitter: https://twitter.com/_CryptoCat
GitHub: https://github.com/Crypto-Cat/CTF
HackTheBox: https://app.hackthebox.eu/profile/11897
LinkedIn: https://www.linkedin.com/in/cryptocat
Reddit: https://www.reddit.com/user/_CryptoCat23
YouTube: https://www.youtube.com/CryptoCat23
Twitch: https://www.twitch.tv/cryptocat23
↢AngstromCTF↣
https://ctftime.org/event/1859
https://2023.angstromctf.com/challenges
https://discord.gg/Dduuscw
https://twitter.com/angstromctf
↢Resources↣
Ghidra: https://ghidra-sre.org/CheatSheet.html
Volatility: https://github.com/volatilityfoundation/volatility/wiki/Linux
PwnTools: https://github.com/Gallopsled/pwntools-tutorial
CyberChef: https://gchq.github.io/CyberChef
DCode: https://www.dcode.fr/en
HackTricks: https://book.hacktricks.xyz/pentesting-methodology
CTF Tools: https://github.com/apsdehal/awesome-ctf
Forensics: https://cugu.github.io/awesome-forensics
Decompile Code: https://www.decompiler.com
Run Code: https://tio.run
↢Chapters↣
Start: 0:00
Patch lib-c (pwninit): 0:20
Test the program functionality: 1:05
Check the binary protections (checksec): 1:37
Analyse decompiled code (ghidra): 3:53
Recap of analysis: 6:51
PwnTools script: 8:40
Setup breakpoints: 14:38
Debug with GDB (pwndbg): 15:33
Heap recap (chunk structure): 16:20
Reviewing vulnerability / exploit: 18:01
Finish PwnTools script: 20:40
Test against remote server: 24:13
Final recap: 25:07
End: 25:56
-
 LIVE
LIVE
LFA TV
12 hours agoLIVE & BREAKING NEWS! | FRIDAY 10/31/25
3,404 watching -
 1:04:43
1:04:43
Crypto Power Hour
11 hours ago $5.83 earnedCrypto Price Swings Explained — What Every Investor Needs to Know
21.6K6 -
 21:31
21:31
Clownfish TV
21 hours agoOG YouTube is Officially ENDING! Employees Offered BUYOUTS?! | Clownfish TV
8.51K24 -
 5:54
5:54
Gun Owners Of America
18 hours agoThe Virginia Election Could Shift The Balance of Power Nationwide
9.72K5 -
 2:00:02
2:00:02
BEK TV
1 day agoTrent Loos in the Morning - 10/31/2025
8.41K1 -
 LIVE
LIVE
The Bubba Army
23 hours agoIs Killing The New Trend??! - Bubba the Love Sponge® Show | 10/31/25
1,377 watching -
 2:25:16
2:25:16
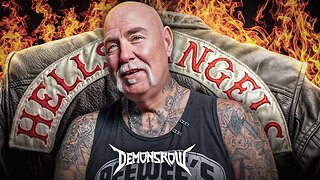
Demons Row
14 hours ago $4.31 earnedEx Hells Angels MC President: Charles “Peewee”Goldsmith (Full Interview)
15.6K4 -
 3:35
3:35
Gamazda
12 hours ago $5.23 earnedThe Darkest Piano Theme?
22.2K38 -
 13:42
13:42
Nate The Lawyer
20 hours ago $4.11 earnedINSANE Judge REMOVED For Lying Under Oath, Insurance Fraud & Stolen Valor
18.9K15 -
 38:32
38:32
Code Blue Cam
1 day agoHow Police Stopped a Potential Church Massacre...
50.3K12