Premium Only Content
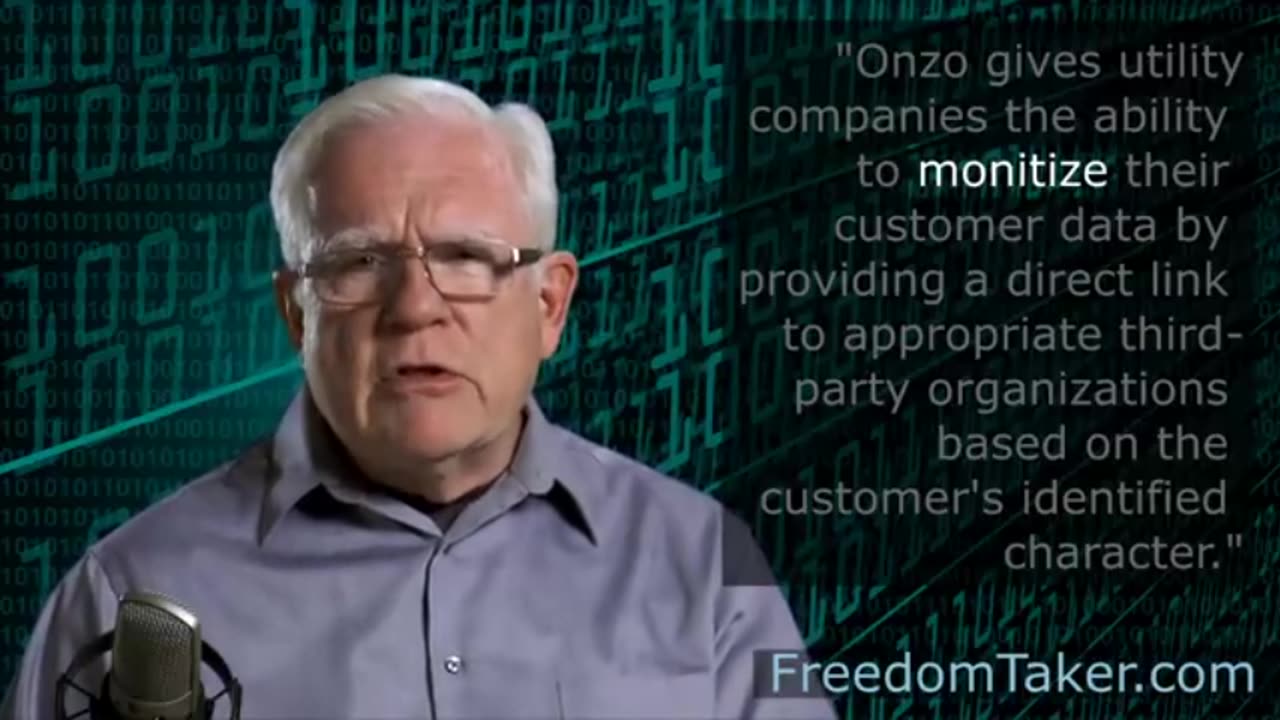
The Role Of Utility Meters In Mass Surveillance
The Role Of Utility Meters In Mass Surveillance
Biometrics
Technologies: Biometric technologies refer to automated methods that are able to identify or recognise the identity of a living person, after analysing some of his/her characteristics (e.g., physiological and/or behavioural characteristics) (Mordini and Petrini 2007; Nwatu 2011). Examples of biometric technologies that consider the physiological characteristics of a person are these of face recognition, facial thermogram, recognition of fingerprints, the geometry of hands, iris or retina scanning, etc. In addition, behavioural oriented biometric technologies include those that can recognise someone’s manner of walking (i.e., gait recognition), analyse the way people type using a keyboard (i.e., keystroke analysis), how they operate a pointing device (e.g., mouse dynamics in the case of a mouse), signature analysis, or even performing a waveform analysis of people’s voices to verify their identity. Finally, another category of biometrics is that of multimodal biometric systems, which refer to systems that include multiple sources in order to establish the identity of an individual (Ross and Jain 2004).
Application areas: The main objective of biometric technologies is to identify, verify, or authorise an individual. That objective is mainly accomplished through the application of pattern-matching algorithms on a set of collected data (usually kept in database systems). Therefore, some of the domains in which biometric technologies find a use are systems applicable to immigration and border control (e.g., use of biometric ‘chipped’ passports (nidirect 2014)); to criminal justice systems and profiling systems (e.g., the Combined DNA Index System (CODIS) (FBI 2011) used by the FBI and U.S. Department of Justice); national identity systems, etc. (Bellanova et al. 2012). Despite the wide spectrum of applications of biometric technologies, their capabilities are mostly restricted to the monitoring of people through identification or verification operations.
Challenges: Despite the high effectiveness of biometric technologies, there are recognised challenges that should be considered when using them. In most of the examined studies, security and privacy concerns are identified as key challenges. Another interesting challenge is that of the reliability level offered by biometric technologies (e.g., reliability with regard to DNA comparison), or even vulnerabilities that might exist in a system operating with biometric technologies (FBI 2006).
-
 15:02
15:02
joegecko's Proxy Channel
11 days agoTexas School CAUGHT Drugging Kids
202 -
 DVR
DVR
Man in America
13 hours agomRNA 2.0: This Frightening Tech Can Target Your BRAIN Using Biological Post Codes
10K4 -
 1:28:31
1:28:31
The Charlie Kirk Show
3 hours agoTHOUGHTCRIME Ep. 100 — Turning Point Halftime? Potatoes and Katie Porter? Hasan the Dog Shocker?
61.9K20 -
 LIVE
LIVE
SpartakusLIVE
4 hours agoNEW Update, NEW Meta || Zombies Mode is BACK - Smokes NURFED
405 watching -
 13:10
13:10
Robbi On The Record
3 hours ago $2.03 earnedThe War on Christians | China’s Surveillance & Nigeria’s Killing Fields
17.3K22 -
 DVR
DVR
Flyover Conservatives
22 hours agoYour Home Just Became a Healing Room — The Truth About Red Light & Med Bed - Jonathan Otto | FOC Show
13.1K2 -
 2:11:35
2:11:35
Mally_Mouse
4 days ago🎮 Throwback Thursday! Let's Play: Kingdom Hearts 1 pt. 2
14K2 -
 3:00:37
3:00:37
Barry Cunningham
6 hours agoBREAKING NEWS: LETITIA JAMES INDICTED FOR MORTGAGE FRAUD!!! LIBTARD TEARS ARE FLOWING!
42.1K24 -
 1:17:42
1:17:42
Glenn Greenwald
6 hours agoUS/Venezuela Escalations: Revisiting Key Developments and the Push for Regime Change | SYSTEM UPDATE SPECIAL
103K141 -
 DVR
DVR
ProvenTactics
3 hours agoFPS Shooter Games
10.6K2