Premium Only Content

Ultimate Vulnerability Scanning Guide for Beginners | CEH v13 Practical ILabs Walkthrough
Uncover the secrets of effective vulnerability scanning in our latest tutorial! Learn how to leverage crucial databases like CVE, CWE, and NVD for in-depth vulnerability research. Follow along as we dive into the practical side, demonstrating step-by-step techniques using renowned scanners – Nessus, Open Vas, and Nikto. Stay ahead of potential threats and strengthen your cyber defenses with this hands-on guide. Don't miss out on the latest tactics for a secure digital landscape in 2023! 💻🔍 #VulnerabilityScanning #CVE #Nessus #OpenVas #Nikto #CybersecurityTutorial
Join CEH v12 Practical Complete Course
https://www.udemy.com/course/ceh-practical/?referralCode=289CF01CF51246BCAD6C
https://cavementech.com/
______________________________________
Get the Udemy courses to get started in practical pen testing and hacking
1. Practical Hacking and Pentesting Course for Beginners
https://www.udemy.com/course/practical-hacking-pentesting-guide/?referralCode=CE0BCED85E7608ACC031
2. Complete Windows password hacking course
https://www.udemy.com/course/crack-windows-passwords/?referralCode=82D81C6B54BA4DB70A15
3. Cracking office files passwords(excel,PowerPoint,word)
https://www.udemy.com/course/office-password-cracking/?referralCode=3AC1F35BD17DC4739BC0
4. CEHV12 Practical certification preparation course with hands on labs
https://www.udemy.com/course/ceh-practical/?referralCode=289CF01CF51246BCAD6C
5. IoT Hands-on Hacking and Pentesting course for beginners
https://www.udemy.com/course/iot-security-beginners/?referralCode=997AF261C2E6F99BC914
6. Practical Malware Analysis for Beginners
https://www.udemy.com/course/practical-malware-analysis-for-beginners/?referralCode=CF1C47BF5371D1B9F20A
_________________________________
Disclaimer
This video is for educational purposes only. The content shared in this course is intended to help viewers understand the basics and practical aspects of ethical hacking. It is not meant to promote or condone any illegal activities, hacking, or malicious behavior. Always adhere to ethical standards and respect privacy when practicing cybersecurity skills.
-
 6:55
6:55
Tactical Advisor
41 minutes agoRadian / Canik Prime Collab Handgun (FIRST LOOK)
2 -
 11:44
11:44
Scammer Payback
1 hour agoLocked Their Hard Drives, Listen to Them Rage
23 -
 30:02
30:02
Rethinking the Dollar
1 hour agoSilver 3‑Bagger in Yen! The Real Money Moves Now | News Update
58 -
 1:46:05
1:46:05
Graham Allen
2 hours agoTrump’s First Year! Trump Agrees To NATO Meeting For Greenland! + Dems Already Destroying Virginia!
125K495 -
 LIVE
LIVE
The Big Mig™
2 hours agoAI, How Do We Protect Humanity w/ The Alliance For Secure AI
2,826 watching -
 1:09:44
1:09:44
Chad Prather
13 hours agoWhen the Gospel Disrupts What We Worship
100K31 -
 17:33
17:33
DeVory Darkins
15 hours agoDemocrats pull DISGUSTING stunt on LIVE TV as rioters seize Minneapolis streets
17.9K80 -
 12:17
12:17
Clintonjaws
11 hours ago $17.60 earnedDon Lemon Has A Melt Down Live On-Air Over DOJ Charges & Nicki Minaj
63.4K84 -
 15:18
15:18
BlackDiamondGunsandGear
13 hours agoIs Glock Gen 6 Worth it?
43.6K6 -
 1:16:25
1:16:25
OHVALUES
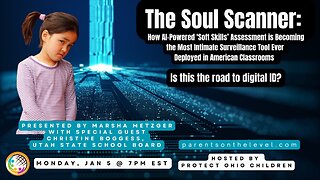
7 days agoExposing SEL: "The Soul Scanner"
48.3K5