Premium Only Content
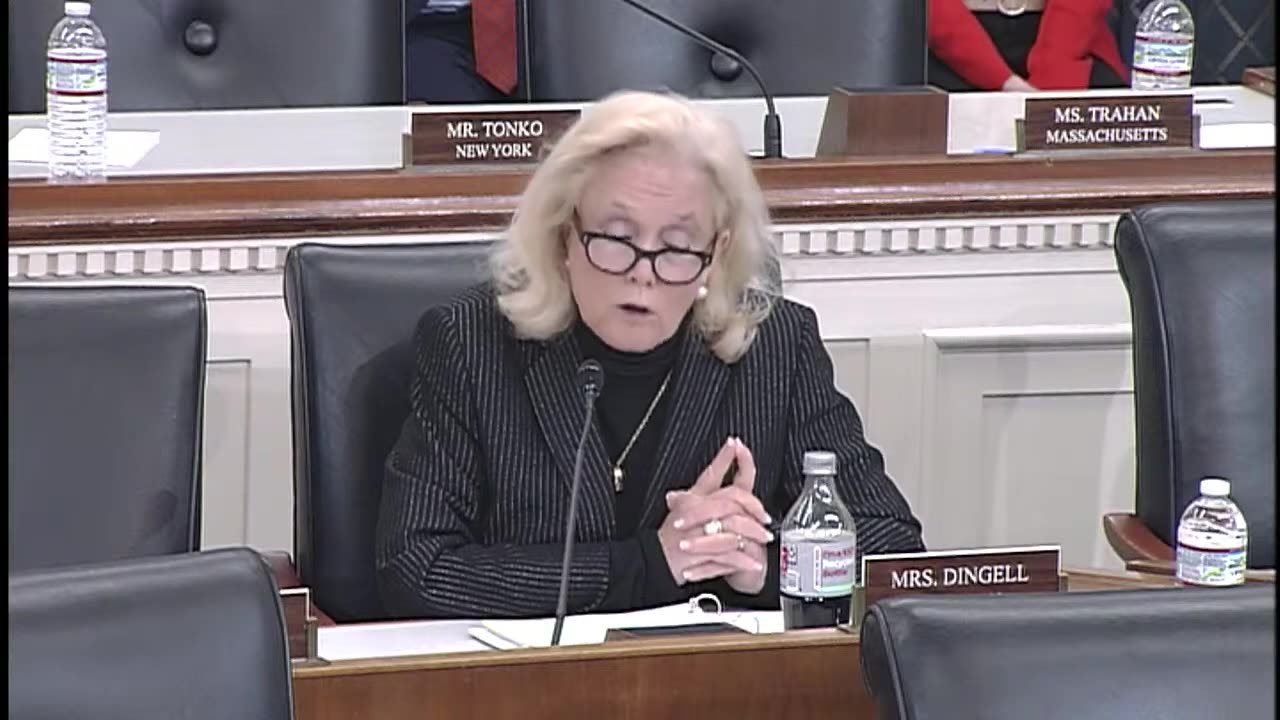
QA ONLY: Cybersecurity Vulnerabilities in Legacy Medical Devices 04-01-25 - Energy & Commerce
00:01:36 How many legacy medical devices are in use across the
00:05:51 Is it easy to manipulate a medical device?
00:08:56 HHS to Cut 20,000 Positions at FDA
00:10:18 What Happened to FDA's First Round of Fires?
00:11:05 How Back Door Medical Devices Can Be Vulnerable
00:16:47 How did cybersecurity experts support the medical device reviewers?
00:17:57 Is there any certainty in the FDA review process?
00:19:25 What challenges do hospitals face because of the differences between
00:22:59 Why cybersecurity risks are unlikely to be sufficiently mitigated through
00:24:50 What role does NIH funding play in the development of
00:29:56 Is there a back door into a medical device?
00:32:09 What Subject Matter Experts Contribute to Medical Device Review
00:34:18 What are some of the challenges of identifying cybersecurity risks
00:38:26 Liability of Failure of a Medical Device for a Cybersecurity
00:39:34 How important is it to the device industry that the
00:39:53 FDA's In-House Expertise on Medical Devices
00:40:42 Doctor Fu: How Important is Maintaining America's Biomedical Research Enterprise?
00:43:28 What tools are available to inform the public and providers
00:45:05 What's the difference between cutting edge and legacy medical devices?
00:48:17 What the FDA's Center for Devices and Radiological Health Can
00:48:35 The main risk in my view is the inconsistency
00:49:19 He is running algorithms in every department he has no
00:52:16 I'll start with you doctor dam if it's likely
00:52:59 Is the entire U.S. Mr. Danoff?
00:56:19 What can be done to make a better cybersecurity with
00:59:57 Ending Advisory Committees at CDC, FDA and CDC
01:01:22 Is the medical device industry the most targeted for cyber
01:02:16 Health Sector Coordinating Council's Cybersecurity Working Group
01:04:54 How to improve the regulations but not make them obstacles
01:06:10 How is firing FDA safety employees an effective way to
01:07:58 What Is Being Done to Address Information Blocking?
01:11:39 Doctor Demuth: Is there a standard curriculum at any medical
Legislators are holding a hearing on cybersecurity vulnerabilities and legacy medical devices. The risk of harm to patients is big is a big concern because if a medical device vulnerability is exploited, the ability for a device to help monitor, diagnose or treat a patient can be compromised. There's also national security concerns.
Summary generated by AI
This is just the direct questions and answers portion of the hearing, not commentary.
Full video at https://www.youtube.com/watch?v=D2kFOgCpfvM.
Let me know if the full video link is down and I'll upload the full version.
-
 2:35:59
2:35:59
Cut to the chase
5 months agoQA ONLY: Assuring Abundant, Reliable American Energy 04-30-25 - Energy & Commerce
153 -
 1:04:23
1:04:23
TheCrucible
4 hours agoThe Extravaganza! EP: 48 (10/06/25)
59.1K6 -
 LIVE
LIVE
Robert Gouveia
1 hour agoTrump Appeals Judicial Takeover!! Churches TARGETED in Info War!
1,243 watching -
 1:38:33
1:38:33
Redacted News
3 hours agoTrump Slams Neyanyahu "Take the Deal, Stop being so F*cking Negative", Hamas responds | Redacted
96.6K116 -
 1:26:52
1:26:52
Kim Iversen
2 hours agoWho Let This Happen??: Israel Now Controls Tik Tok, CBS News, HBO, MTV and More
22.6K34 -
 LIVE
LIVE
Dr Disrespect
7 hours ago🔴LIVE - DR DISRESPECT - BLACK OPS 7 - GIVE ME BACK MY NUKE
1,164 watching -
 1:30:22
1:30:22
Tucker Carlson
6 hours agoEverything You Should Know About Dan Crenshaw, How He Got Rich & Why He’s So in Love With Ukraine
50.8K111 -
 LIVE
LIVE
Wayne Allyn Root | WAR Zone
7 hours agoWatch LIVE: The War Zone Podcast with Wayne Allyn Root
35 watching -
 LIVE
LIVE
Total Horse Channel
3 days agoGypsy Georgia National Fair Show
22 watching -
 LIVE
LIVE
The Amber May Show
2 hours agoThe Shocking Truth Inside the Democrats’ Spending Bill
71 watching
